Phishing didn’t evolve by accident.
It evolved because defenders optimized for the wrong signals.
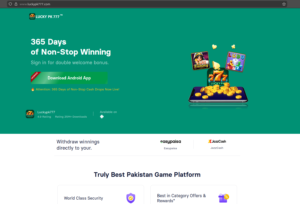
Domains like luckypk777[.]com and luckypk777d[.]com don’t look like classic phishing. They don’t need to. They hide behind brand trust, payment rails, and human psychology; the exact blind spot that all of the legacy security stacks still conveniently ignore.
This is the anatomy of one such mass phishing operation and why PhishReaper exists to dismantle it.
The Problem: We’re Still Hunting Pages. Attackers Are Hunting People.
Most phishing defenses are still page-centric:
-
Block known bad domains
-
Scan HTML for forms
-
Match signatures
-
Wait for abuse reports
But luckypk777d[.]com isn’t built to fail those checks. It’s built to manipulate intent.
At PhishReaper, we don’t ask “is this page fake?”
We ask:
“What is this domain trying to make the user do?”
That question changes everything.
Phase 1: Brand Abuse Without Brand Infrastructure
luckypk777d[.]com claims association (partnership) with JazzCash without touching JazzCash systems, APIs, or domains. On the contrary, it is a convenient redirect through many of the brand impersonation domains targeting JazzCash such as jazzcashd[.]com, jazzcashapkk[.]com, jazzcashx[.]com
This is deliberate.
Attackers know:
-
Brand takedowns are slow (practically non-existent in this particular case since some of these impersonation domains are several months old)
-
Legal enforcement lags
-
Visual trust beats technical truth
PhishReaper flags this immediately because:
-
The domain claims brand authority
-
The brand has no technical relationship with the domain
-
The context (casino + wallet) violates normal brand behavior
This is brand-intent mismatch, not just impersonation.
Phase 2: Casino as a Phishing Delivery Mechanism
The casino is not the only scam.
The casino is also the delivery system.
It normalizes:
-
Deposits
-
Repeated payments
-
Loss acceptance
-
Manual payment steps
This is where legacy scanners fail — because there is no obvious credential harvest page.
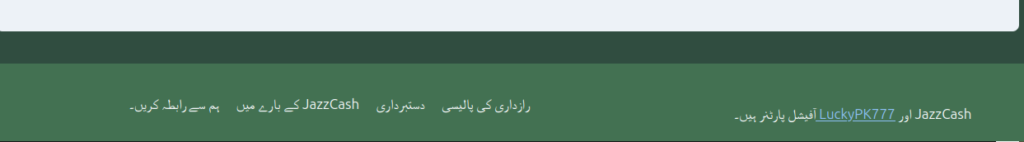
PhishReaper models this as staged intent escalation, as described in steps here:
The phishing happens after the user is comfortable.
Phase 3: Payment-Rail Deception (The Real Kill Chain)
Logos are cheap.
APIs are expensive.
These sites impersonate payment acceptance, not integration.
What users see:
-
JazzCash logo
-
“Pay with JazzCash”
-
Familiar workflow language
What actually happens:
-
Off-platform transfers
-
Socially engineered OTP requests
-
Manual wallet interactions
PhishReaper detects this by correlating:
-
Claimed payment rails
-
Absence of real payment endpoints
-
Behavioral divergence from legitimate merchant flows
This is not phishing as a page. This is phishing as a transactional trap.
Phase 4: Victims as Distribution (Why This Scales)
Referral mechanics turn users into infrastructure:
-
Invite codes
-
Share bonuses
-
Group infiltration
- Social media integrations within the games
Now the attacker doesn’t need:
-
Ads
-
Spam
-
Infrastructure growth
They get organic lateral movement.
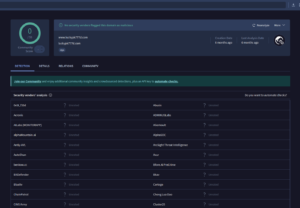
PhishReaper tracks this by:
-
Mapping sibling domains
-
Correlating referral language
-
Linking behavioral clusters across campaigns
This is how we identify operator-level activity, not just domains.
Why Traditional Defenses Miss This Entirely
| Legacy Approach | Why It Fails |
|---|---|
| Blocklists | Domain churn beats them |
| SSL checks | SSL is meaningless now |
| Static scanners | No obvious form harvest |
| User awareness | Trust is already established |
| Brand takedowns | Too slow, too narrow |
This attack isn’t loud.
It’s patient. Unfortunately, victims were never the priority in the legacy detection models by design.
What PhishReaper Does Differently
PhishReaper was built for intent-first threat hunting.
We:
-
Track brand abuse without requiring brand compromise
-
Detect phishing before credentials are requested
-
Correlate infrastructure, behavior, and psychology
-
Identify campaigns, not just domains
We don’t wait for theft. We detect pre-theft conditions.
Why This Matters
Domains like luckypk777[.]com andluckypk777d[.]com aren’t edge cases.
They’re the blueprint.
Tomorrow it won’t be JazzCash. It’ll be another wallet, another bank, another brand users trust.
If your defense strategy only reacts after damage occurs, you’re already behind.
PhishReaper exists because phishing is no longer a page problem.
It’s an intent problem.
And intent leaves fingerprints.





Leave a Reply